
After you’ve been notified of a data breach, you should contact your bank and the three major credit bureaus as soon as possible.
The information provided on this website does not, and is not intended to, act as legal, financial or credit advice. See Lexington Law’s editorial disclosure for more information.
When a data breach occurs, you should monitor all of your accounts for suspicious activity. Creating alerts for your banking accounts can help you react to suspicious transactions. A similar strategy is advised for your credit report; in certain cases, companies will have to provide credit monitoring services to their customers for up to 12 months.
Data breaches can lead to negative situations, such as identity theft and credit card fraud. Below, we’ll discuss what to do after a data breach occurs and explore options for reliable credit monitoring services.
Key takeaways:
- A data breach occurs when cybercriminals illegally gain access to sensitive information.
- In certain cases, companies will be ordered to provide credit monitoring services to their customers for up to 12 months.
- The Equifax® data breach of 2017 compromised 148 million Americans and 15 million British citizens.
Table of contents:
- What is a data breach?
- How do you check if your personal information was exposed?
- What should you do after a data breach?
- What states have data breach laws?
- 3 reasons data breaches happen
- Monitor your credit with Lexington Law Firm
What is a data breach?
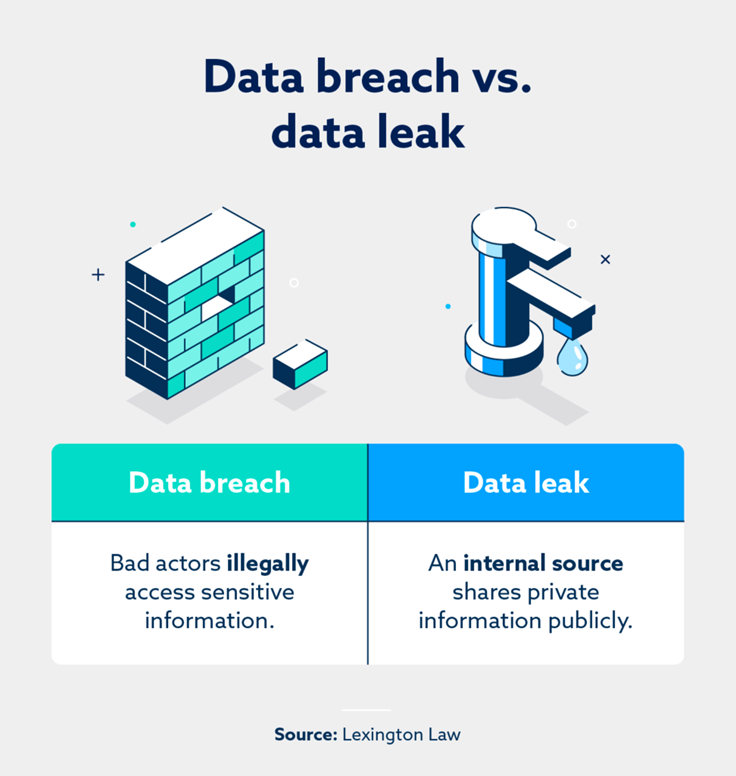
A data breach occurs when cybercriminals and bad actors illegally access sensitive data. A data breach can happen to specific individuals and large organizations—such as the 2017 Equifax data breach, which impacted nearly 150 million Americans and 15 million British citizens.
If an organization is held accountable for a data breach by a court of law, compensation may be issued to victims. For example, the Equifax breach settlement was finalized in January 2022 and resulted in free credit monitoring services and up to $425 million of support to impacted individuals.
How do you check if your personal information was exposed?
The Data Breach Notification Act offers guidelines and regulations in the event of a data breach. Section 2 of this act states that businesses and federal agencies must tell affected individuals that their data has been leaked “without unreasonable delay.”
These specific guidelines are relevant after a data breach occurs. Here are several actionable steps if you want to take proactive measures to combat a data breach:
- Intrusion detection system (IDS): This technology can monitor a network and determine if suspicious or malicious activity is underway.
- Data leak checker websites: Websites like Have I Been Pwnd will help you check if one of your emails was part of a data breach.
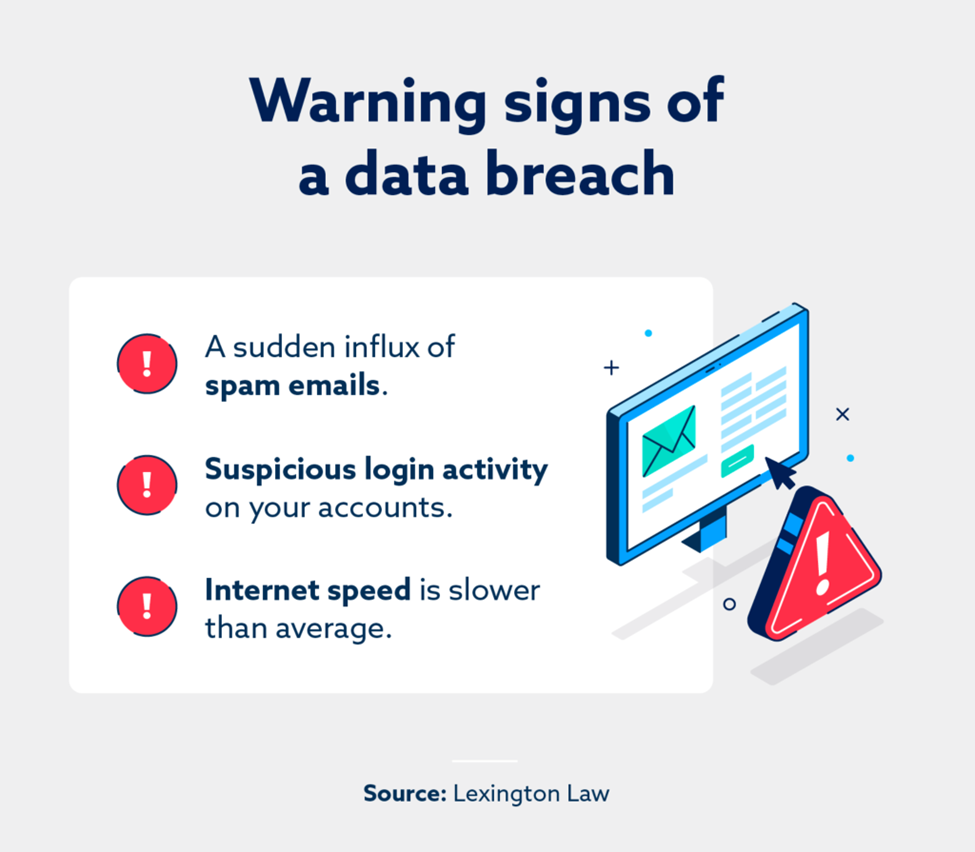
- Review your emails: If your spam and junk email boxes have an unusual amount of spam, your email could’ve been compromised.
What should you do after a data breach?
After you’ve received a notice that your data was compromised, it’s natural to feel overwhelmed or upset by this violation of your privacy. Nevertheless, taking action and making adjustments is the best way to minimize or prevent the worst outcomes.
Change your passwords
If you were part of a data breach, there’s a high likelihood that cybercriminals might possess your current login information. Changing your passwords can prevent bad actors from signing into your accounts.
Ideally, it’s best to use a complex password comprising upper and lowercase letters, special characters and numbers. The less this new password resembles your old one, the better. Furthermore, changing your password every few months is an excellent preventive measure.
Activate two-factor authentication (2FA)
Two-factor authentication (2FA) is an additional login step where users have to finish signing in on a trusted device, usually a smartphone. 2FA reduces the likelihood of a bad actor illegally accessing one of your accounts as the additional login measure (your phone) is on your person.
Look into credit monitoring services
For those wondering what credit monitoring is, the term refers to any service that watches your credit reports and alerts you about suspicious activity that doesn’t match your usual financial habits.
Credit monitoring services look for everything from fluctuations in your credit score to new accounts that have been opened in your name. Lex OnTrack is a monitoring service that tracks your credit history and helps protect your identity from fraud.
Freeze your credit with the three credit bureaus
Learning how to freeze your credit can help you stop cybercriminals from taking unauthorized actions with your credit. To fully freeze your credit, you’ll at least want to contact Equifax®, Experian® and TransUnion®—the three major credit bureaus.
Contact your bank
Speaking with your bank after you’ve been notified of a data breach is an effective way to protect your finances. You’ll have an opportunity to notify your financial institution of this unfortunate event, and you’ll also be able to review recent account activity.
If recent purchases were made on your account that don’t align with your habits, they could be tied to unlawful activity.
What states have data breach laws?

Every state in America has cybersecurity laws that protect civilians, organizations and federal agencies in the event of a data breach. The Data Breach Notification Act generally applies to all 50 states alongside territories and districts.
At the time of writing, California, Colorado, Connecticut, Utah and Virginia have unique data privacy laws that differ somewhat from their contemporaries. For instance, the California Consumer Privacy Act (CCPA) gives Californians the right to demand all information that a company and its third-party partners have on them.
3 reasons data breaches happen
Data breaches are incredibly alarming, and it’s tempting to search for an easy explanation as to why they happen. Though only a small number of them are successful, cyberattacks are quite common.
A study by the Clack School found that some computers may be attacked, on average, approximately 2,200 times each day. Some factors that raise the odds of a cyberattack succeeding are outlined below.
1. Malware attacks
Malware (or malicious software) can compromise security if someone downloads it onto their device. For example, a key logger is a type of malware that records every keystroke a user inputs. Such software could help cybercriminals steal admin credentials from an organization, then log in and access sensitive data.
2. Internal data leak
“What is a data leak?” is a fair question, as this term sounds similar to a data breach. However, a data leak occurs when an internal source releases private information to the general public. If someone working at an organization gives out confidential login details, a cybercriminal could capitalize on that and initiate a data breach.
3. Outdated software
Software updates bolster a network’s security and make it harder for hackers to slip past defenses. Repeated cyberattacks that are launched against systems with outdated software are more likely to be successful.
Monitor your credit with Lexington Law Firm
The sheer number of cyberattacks that occur each day can be alarming, but there are many ways to protect yourself from digital disturbances. A credit monitoring service is an excellent tool that works in the background and catches seemingly minute details.
Explore Lexington Law’s services, which include credit monitoring as well as assistance with challenging errors on credit reports, if any are found.
Note: Articles have only been reviewed by the indicated attorney, not written by them. The information provided on this website does not, and is not intended to, act as legal, financial or credit advice; instead, it is for general informational purposes only. Use of, and access to, this website or any of the links or resources contained within the site do not create an attorney-client or fiduciary relationship between the reader, user, or browser and website owner, authors, reviewers, contributors, contributing firms, or their respective agents or employers.
